Individuals holding positions with access to national security technology are the predominant targets for internal theft of such technology.
In the latest episode of "The Federal Drive," our unnamed host delves into the current risks small businesses and universities face regarding corporate espionage in a rapidly distributed national innovation network.
Joining our discussion are Michael Crouse, who chairs INSA's insider threat subcommittee, and John Doyon, Executive Vice President of the Intelligence and National Security Alliance.
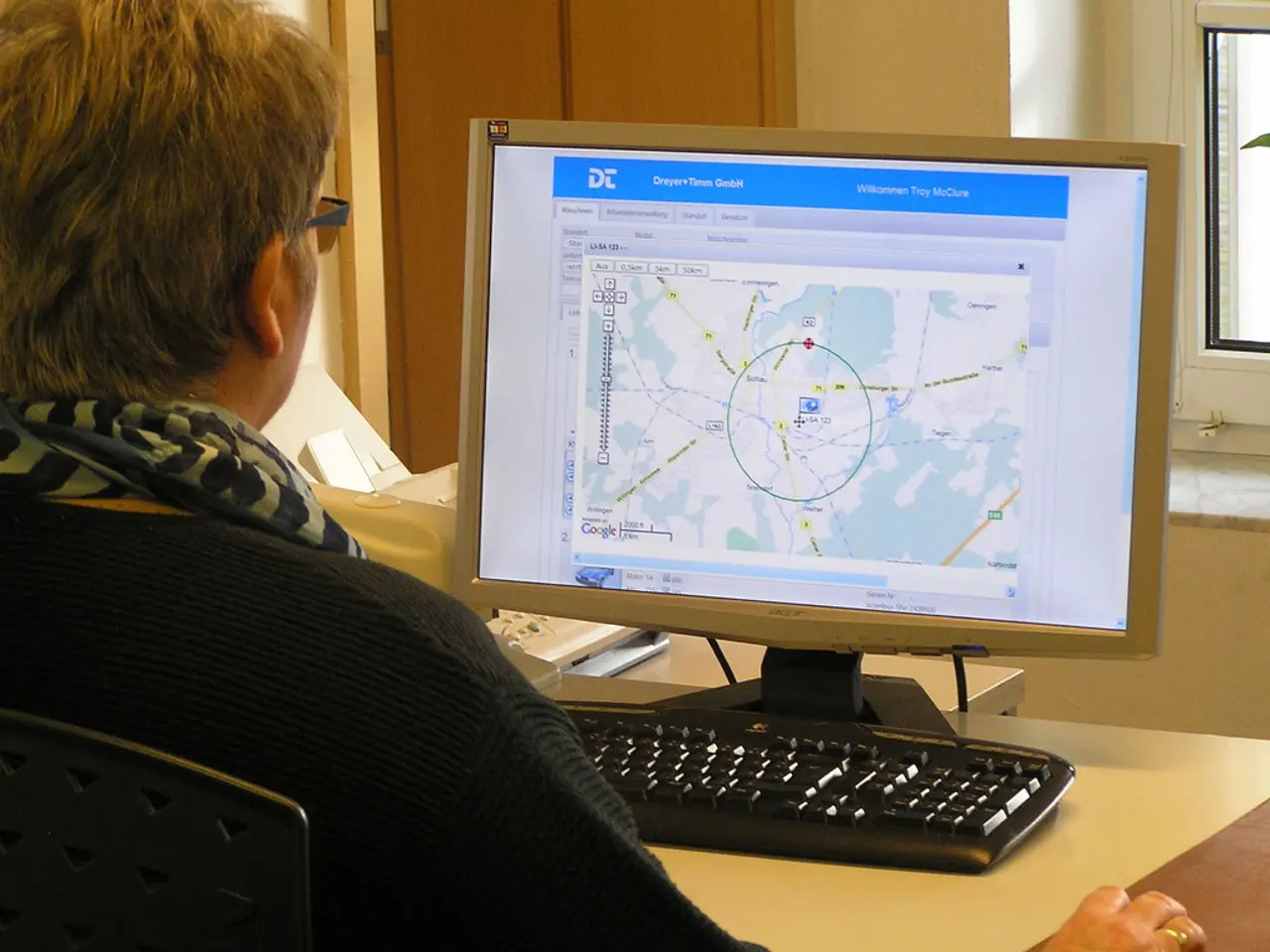
The distributed national innovation network, characterized by its expansive reach and collaborative nature, has unfortunately become a prime target for cybercriminals, foreign adversaries, and espionage efforts. Key risks include cyberattacks and cyber espionage targeting intellectual property, financial and reputational damage from breaches, risks of espionage via IoT and misconfigured cloud services, international espionage and technology theft, and risks from funding and collaborative networks.
Small and midsize businesses (SMBs) and research institutions have become particularly vulnerable, with many lacking adequate cybersecurity measures and response plans. In 2025 alone, nearly 60% of SMBs experienced cyberattacks, often resulting in significant financial losses and damage to trust in institutions.
To combat these threats, experts and policymakers advocate a multi-faceted approach. This includes strengthening cybersecurity hygiene and awareness, adopting advanced security technologies, implementing policy and legislative measures, enhancing supply chain and partnership vetting, securing cyber insurance and regulatory compliance, and addressing physical security and insider threat mitigation.
The INNOVATE Act, for instance, aims to introduce due diligence standards for screening companies receiving government innovation funding to prevent foreign espionage infiltration. Meanwhile, universities and small businesses should rigorously assess foreign ties and control information sharing within distributed networks to reduce exposure.
As the federal community navigates this complex landscape, "The Federal Drive" offers expert insights on current events, keeping readers informed and up-to-date with daily news and analysis affecting the federal workforce. For more interviews, visit our website.
Remember, corporate espionage is a pressing concern in the context of a more distributed national innovation network. To reach our team with feedback and story ideas, please contact us at FederalDrive@our website.
[1] Cybersecurity Ventures [2] Verizon 2021 Data Breach Investigations Report [3] U.S. Senate Committee on Small Business & Entrepreneurship [4] CISA - Securing IoT Devices [5] Office of the Director of National Intelligence - Foreign Spies Stealing US Secrets
- To address the growing concern of cyber espionage in the federal workforce, particularly in the small-business sector, policymakers and experts recommend adopting a multi-faceted approach, which includes securing cyber insurance and regulatory compliance, strengthening cybersecurity hygiene and awareness, implementing policy and legislative measures, such as the INNOVATE Act, and rigorously assessing foreign ties within distributed networks.
- In the wake of increasing cyberattacks on small and midsize businesses (SMBs),schedules should be arranged to review the Verizon 2021 Data Breach Investigations Report for insights on best practices in cybersecurity, and resources like CISA's guide on Securing IoT Devices could be utilized to bolster the security of interconnected devices and cloud services.